
With the average cost of a data breach at $4.88 million1, cybersecurity threats are a growing concern for businesses of all sizes. From phishing scams to ransomware attacks, companies without a robust IT security plan are at risk of significant financial loss. Cybersecurity awareness training is no longer optional but essential for protecting your employees, customers, and bottom line.
In this guide, we explain key cybersecurity training principles every business and all employees should know to keep your organization safe.
Table of Contents:
What Is Cybersecurity Awareness Training?

In a world where one cyberattack happens every 39 seconds, the last thing business owners want is to be left defenseless when disaster strikes.2 Just as fire drills prepare your team for emergencies, cybersecurity awareness training teaches employees how to identify, prevent, and report cyber threats.
Using hands-on exercises based on real-world situations, these educational programs equip them with essential skills and best practices for handling phishing scams, passwords, data treatment, and more. These practices create an agile, security-conscious workplace that reduces your organization’s vulnerability to cyberattacks.
The Importance of Cybersecurity Awareness
Assuming every employee understands cybersecurity without training is like expecting someone to put out a fire without an extinguisher. Without establishing the right protocols, your entire organization is vulnerable to:
- Data loss: Cyberattacks can destroy or exploit sensitive company data, which has a multitude of logistical, financial, and reputational consequences.
- Insider threats: Employees can knowingly or unknowingly become a vector for attacks, either by mishandling data or falling for scams that let hackers access your systems.
- Downtime: Cyberattacks can slow or stop operations entirely for any amount of time—and over 60% of downtime costs more than $100,000.3
- Financial loss: Beyond the cost of downtime, cybercriminals can demand ransoms of up to $2 million on average.4 Excluding ransoms, the average recovery cost for cyberattacks is $2.7 million.
- Damaged reputation: You can’t put a price tag on the value of reputation. Cybersecurity breaches can have a long-term impact on trust, costing you customers and revenue.
With comprehensive cybersecurity training programs, your organization can establish clear guidelines for both responding to threats and preventing them with good digital habits.
7 Cybersecurity Principles Your Employees Need to Know
Cyber threats exist whether you are prepared or not—but with proper training, your team can learn to recognize risks, protect sensitive data, and help defend your business. Below are some of the top cybersecurity principles your employees need to know.
1. Recognizing Social Engineering Techniques
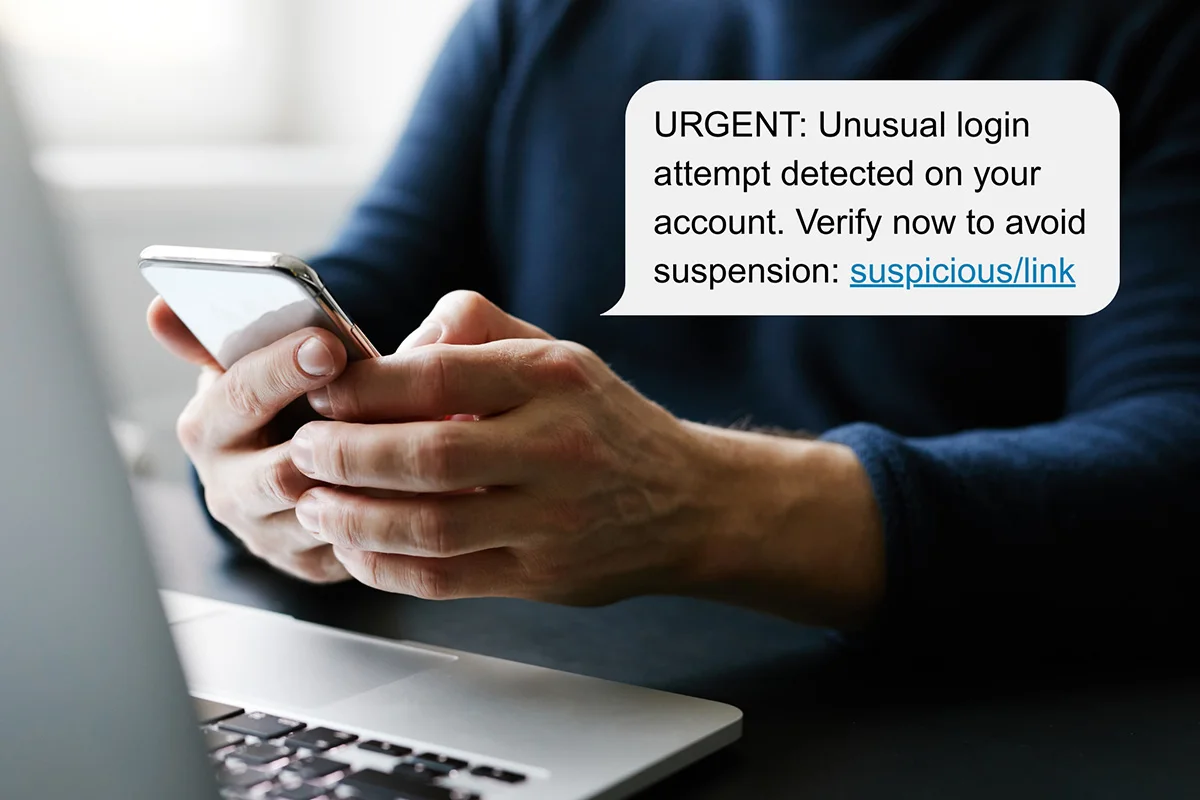
Social engineering is a cybercrime tactic that uses psychological manipulation to pressure people into revealing sensitive information. According to Verizon’s 2024 Data Breach Investigations Report, 68% of breaches involved a non-malicious human element—including falling for social engineering tactics.5
Some examples of social engineering tactics include:
- Pretexting: Attackers fabricate convincing scenarios to extract sensitive data
- Impersonating authority figures: Attackers pose as executives, IT staff, or law enforcement to pressure victims into compliance
- Creating a sense of urgency: Scammers trick victims into acting quickly before they have time to verify legitimacy
- Using fear tactics: Hackers threaten victims with consequences like legal trouble or account suspension
- Building trust: Attackers build false trust by pretending to be a colleague, vendor, or friend
- Quid-pro-quo: Scammers offer something in return, such as a refund, in exchange for the victim’s compliance
Many of today’s cybercrimes rely on social engineering tactics, which is why it’s so important for your team to know how to recognize these attempts and verify identities before transferring sensitive data.
2. Recognizing and Avoiding Phishing Attacks

Phishing is one of the most common cyber threats, where cybercriminals contact you directly and use social engineering to steal data or access computer systems. Phishing usually happens in the form of emails, SMS messages, and phone calls.
On average, 75% of cybersecurity threats arrive through email-based phishing attacks.6 Sometimes these messages are highly targeted and include personal details to seem more convincing, a tactic known as spear phishing.
Cybersecurity training can teach your employees how to recognize suspicious messages and avoid even the most sophisticated phishing scams, greatly reducing your organization’s vulnerability to cyber-attacks.
3. Preventing Malware and Ransomware Attacks
Another essential aspect of cybersecurity training is educating employees about the risks of malware and ransomware attacks:
- Malware is malicious software that causes damage, steals data, or disrupts infiltrated systems. It mainly spreads through phishing, infected downloads, or malicious websites.
- Ransomware is a type of malware that locks or encrypts files, demanding payment in exchange for restored access. Nearly one-third of data breaches in 2024 involved ransomware.5
A recent study found that 63% of ransomware payments were $1 million or more.4 And with 55.8% of ransomware attacks targeting organizations with under 50 employees, it’s especially important for small businesses to stay vigilant against ransomware threats.7
4. Strong Passwords and Login Safety Practices

According to Google Cloud’s Threat Horizons report, weak passwords account for nearly half of all data breaches.8 Fortunately, cybersecurity training is a great way to educate employees about strong password habits and login safety.
Some essential password best practices your employees should know:
- Use unique, complex passwords for every account
- Never use the same login credentials across multiple platforms
- Enable multi-factor authentication (MFA) whenever possible for extra security
- Use a password manager software to store and generate credentials within your organization
5. Safe Browsing Practices

Cybercriminals often create fake websites designed to steal information or spread malware. Cybersecurity training teaches employees how to spot these threats and browse safely to protect company data.
Safe browsing practices include:
- Only enter sensitive data on sites that start with “https” (the “s” means secure)
- Watch for misspellings in website names, strange URLs, and fake security warnings
- Never download unverified software or browser extensions
- Avoid clicking on pop-ups that ask for logins, downloads, or sensitive data
6. Protecting Sensitive Business Data

All employees within your organization should understand how to classify and treat business data. This includes understanding exactly what type of data should remain confidential.
Examples of confidential data:
- HIPAA/PHI (Protected Health Information): Any health-related information, such as medical records, billing information, insurance policy numbers, etc.
- Personal Identifiable Information (PII): Social security numbers, birthdays, or addresses
- Intellectual Property (IP): Trade secrets, patents, or product designs
- Financial data: Financial information like bank statements, balance sheets, cash flow, profit & loss statements, etc.
Cybersecurity training also teaches employees how to properly treat confidential data within your organization’s digital environments. This includes using proper encryption and access controls, limiting access to sensitive data based on job roles, and regularly backing up data so it can be recovered if needed.
7. Artificial Intelligence (AI) Security Best Practices

Today, over 60% of workers use generative artificial intelligence (AI) tools to complete daily tasks.9 However, this growing adoption means there are new cyber threats to look out for.
For generative AI tools like ChatGPT and Gemini, conversations are reviewed by real humans to help ensure quality and advance the products. This means you should never feed confidential data to AI tools or share anything you don’t want another person to see. Generative AI is also helping social engineering techniques become more advanced and convincing, putting phishing attacks at an all-time high.
Cybersecurity training helps your employees understand the importance of AI safety, protecting your organization from emerging cyber threats.
Cybersecurity Awareness Training for Businesses in Sonoma County
Cybersecurity awareness training is essential for businesses looking to protect their employees, customers, and bottom line. At True IT, we’re proud to offer an interactive, user-friendly cybersecurity awareness training program to businesses across Sonoma County. With more than 40 years of experience, our goal is to equip your staff with everything they need to protect your organization from emerging cyber threats.
81% of organizations train their employees to recognize and report cybersecurity threats.7 Your competitors are prepared—are you?
Contact us online today or call (707)-755-5858 to schedule a FREE consultation with our IT experts.
References
- Cost of a data breach 2024 | IBM. (n.d.). https://www.ibm.com/reports/data-breach
- Cybersecurity: a global priority and career opportunity. (n.d.). University of North Georgia. https://ung.edu/continuing-education/news-and-media/cybersecurity.php
- Uptime Institute’s 2022 outage analysis finds downtime costs and consequences worsening as industry efforts to curb outage frequency fall short. (n.d.). Uptime Institute. https://uptimeinstitute.com/about-ui/press-releases/2022-outage-analysis-finds-downtime-costs-and-consequences-worsening
- Sophos. (n.d.). Cybersecurity as a service delivered | Sophos. SOPHOS. https://www.sophos.com/en-us/press/press-releases/2024/04/ransomware-payments-increase-500-last-year-finds-sophos-state
- Verizon. (2024). 2024 Data Breach Investigations Report. Verizon. https://www.verizon.com/dbir
- OPSWAT, Inc. (2024, December 3). 2024 Osterman Report – OPSWAT. OPSWAT. https://www.opswat.com/osterman-report
- Hornetsecurity. (2024, December 17). Hornetsecurity Q3 2024 Ransomware Attacks Survey – HornetSecurity – Next-Gen Microsoft 365 Security. Hornetsecurity – Next-Gen Microsoft 365 Security. https://www.hornetsecurity.com/en/blog/ransomware-attacks-survey-2024/
- Google Cloud Threat Horizons Report. (n.d.). H2 2024 Threat Horizons Report. In Threat Horizons (p. 2). https://services.google.com/fh/files/misc/threat_horizons_report_h2_2024.pdf
- AI study: Over 60 per cent use Artificial Intelligence at work – almost half of all employees are worried about losing their jobs. (2023, August 28). Deloitte. https://www.deloitte.com/ch/en/about/press-room/ai-study-almost-half-of-all-employees-are-worried-about-losing-their-jobs.html



Comments